Designing a robust authentication mechanism within a distributed architecture requires precision. When moving from a monolithic structure to microservices, the user login process becomes a complex chain of interactions across multiple boundaries. A single failure point can disrupt the entire access management system. To navigate this complexity, engineers rely on sequence diagrams to map out the exact flow of messages between services. This guide provides a deep dive into modeling a user login flow, focusing on clarity, security, and reliability.
📊 Why Sequence Diagrams Matter in Distributed Auth
In a monolithic application, the login logic often resides within a single codebase. The database, the business logic, and the presentation layer share memory and context. However, in a microservices environment, these responsibilities are split. The client does not talk to a single backend; it communicates through gateways, and those gateways route requests to specific services like the Identity Service, the Token Service, or the User Profile Service.
Without a visual representation of these interactions, teams face significant challenges:
- Hidden Latency: Developers may not realize how many network hops occur during a single login attempt.
- Error Propagation: It becomes unclear which service is responsible for specific failure states.
- Security Gaps: Token validation steps might be skipped or duplicated across services.
- Onboarding Friction: New engineers struggle to understand the data flow without a clear map.
A sequence diagram resolves these issues by placing time on the vertical axis. It shows exactly when a request is sent, when a response is received, and what intermediate processes occur. This visualization is not just documentation; it is a blueprint for implementation.
🏗️ Architectural Components Overview
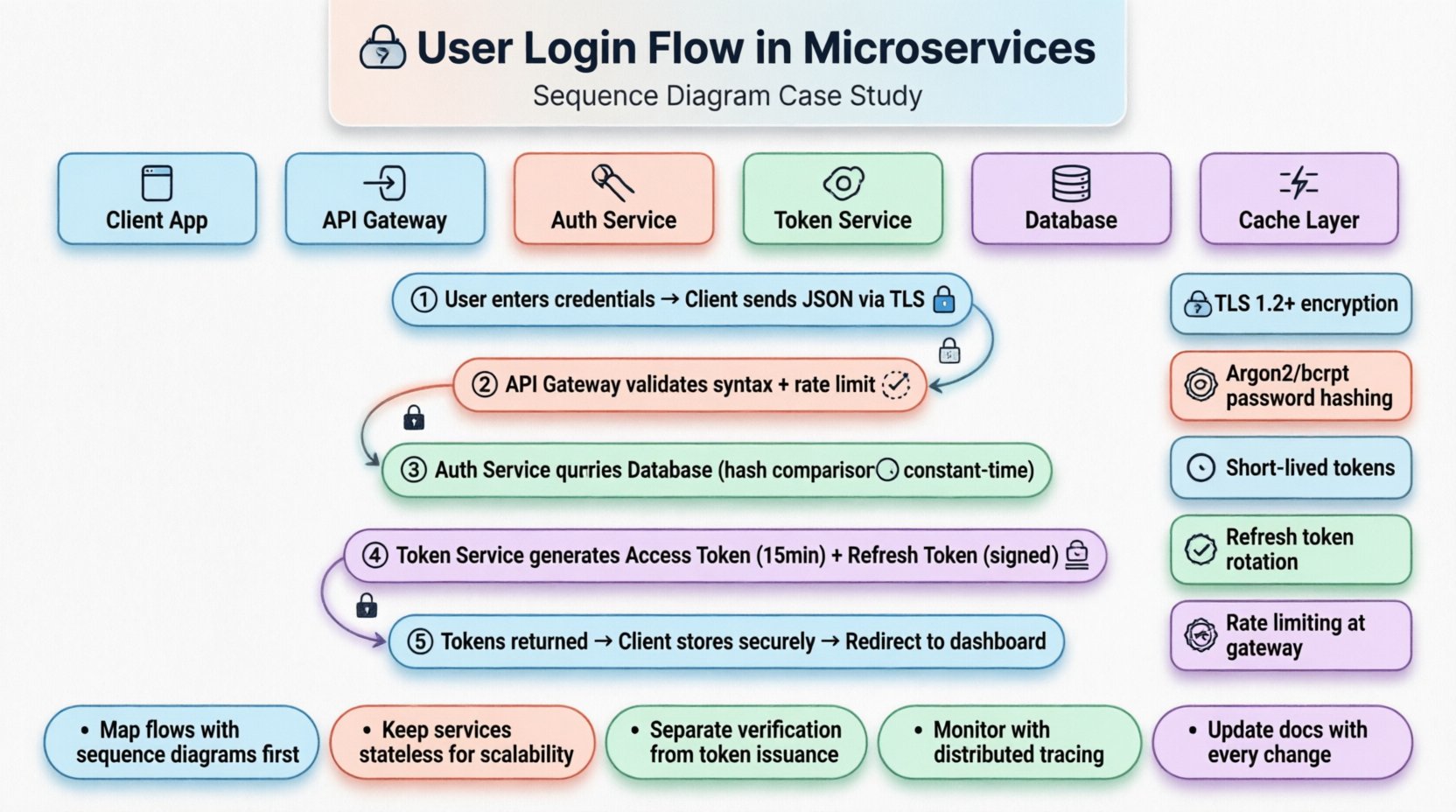
Before diving into the flow, we must define the actors involved in the system. Each component has a specific duty that ensures the integrity of the login process.
- Client Application: The interface where the user enters credentials. It initiates the request and renders the final status.
- API Gateway: The entry point for all external traffic. It handles rate limiting, SSL termination, and initial routing.
- Authentication Service: Validates the user credentials against stored data. It does not issue long-term tokens.
- Token Service: Generates and signs access and refresh tokens after successful verification.
- Database: Stores user credentials, session states, and permission sets.
- Cache Layer: Stores frequently accessed user sessions or token blacklists to reduce database load.
Understanding these roles helps in mapping the sequence diagram accurately. Each arrow in the diagram represents a network call or an internal function call.
🔑 Step-by-Step Login Sequence Analysis
The following breakdown details the logical flow of a standard login request. This sequence assumes a stateless architecture where the client must present a token with every subsequent request.
1. Credential Submission
The user enters their username and password into the client application. The application constructs a JSON payload containing these credentials. It does not send this data directly to the Authentication Service. Instead, it routes the request through the API Gateway.
- The Gateway validates the request structure (syntax check).
- The Gateway checks if the IP address is blocked or rate-limited.
- The Gateway forwards the request to the Authentication Service endpoint.
2. Verification Process
Upon receiving the request, the Authentication Service initiates the verification logic. This is a critical security boundary.
- The service queries the Database to retrieve the user record based on the provided username.
- If no record exists, the service returns a generic error to prevent user enumeration.
- If a record exists, the service retrieves the stored hash of the password.
- The service computes the hash of the input password and compares it with the stored hash.
During this phase, the Authentication Service must ensure that the comparison happens in constant time to prevent timing attacks. A successful match triggers the next step.
3. Token Generation
Once credentials are verified, the Authentication Service signals the Token Service. This separation of concerns is vital for scalability.
- The Token Service generates a short-lived Access Token.
- The Token Service generates a long-lived Refresh Token for re-authentication.
- Both tokens are signed using a private key known only to the Token Service.
- The expiration time is set according to security policies (e.g., 15 minutes for access).
4. Response Transmission
The Authentication Service packages the tokens and sends them back to the API Gateway. The Gateway then forwards this response to the Client Application.
- The Client Application stores the tokens securely (e.g., in memory or secure storage).
- The Client Application stores the Refresh Token for future use.
- The Client Application redirects the user to the dashboard.
📋 Service Responsibility Matrix
To maintain clarity during development and maintenance, teams often use a table to define responsibilities. This ensures no two services attempt to handle the same task.
| Component | Primary Responsibility | Secondary Responsibility | Failure Handling |
|---|---|---|---|
| Client Application | Collecting user input | Token storage | Display generic error messages |
| API Gateway | Routing requests | SSL Termination | Return 503 Service Unavailable |
| Authentication Service | Verify credentials | Lockout management | Log attempt, do not reveal data |
| Token Service | Sign and issue tokens | Key rotation management | Fail secure (deny access) |
| Database | Store user data | Index optimization | Replication fallback |
🔒 Security Implementation Details
Security is the backbone of the login flow. Every step in the sequence diagram must be scrutinized for potential vulnerabilities.
- Transport Security: All communication between the client and the gateway, and between internal services, must use TLS 1.2 or higher. This prevents man-in-the-middle attacks.
- Password Storage: Passwords should never be stored in plain text. Use algorithms like Argon2 or bcrypt with a unique salt per user.
- Token Expiration: Access tokens should have a short lifespan. If a token is stolen, the window of opportunity for an attacker is minimized.
- Refresh Token Rotation: Every time a refresh token is used, a new one should be issued. This limits the usability of stolen refresh tokens.
- Rate Limiting: The API Gateway must enforce rate limits on the login endpoint to prevent brute-force attacks.
When modeling the sequence diagram, explicitly mark these security checks. For example, draw a dashed line indicating a TLS handshake before the request payload is processed.
⚡ Performance and Latency Considerations
In a microservices environment, latency is cumulative. Each service call adds network overhead. The login flow must be optimized to ensure a smooth user experience.
- Database Indexing: Queries for usernames must be indexed to ensure O(log n) lookup times.
- Connection Pooling: Services should maintain connection pools to the database to avoid the overhead of establishing new connections for every request.
- Async Processing: If the login triggers non-critical tasks (like sending a welcome email), these should be handled asynchronously via a message queue, not synchronously within the login flow.
- Caching: User session data can be cached in an in-memory store to speed up subsequent requests, provided the cache is invalidated correctly upon logout.
When analyzing the sequence diagram, look for “wait” states. If the Token Service waits for the Database to confirm a user exists, that is a synchronous dependency that adds latency. Consider if this step can be optimized.
⚠️ Common Implementation Errors
Even experienced teams encounter issues when modeling these flows. Being aware of common pitfalls helps in avoiding them during the design phase.
- Chatty Protocols: Using too many small requests instead of a batched request increases network overhead. For example, requesting user profile data and permission data separately during login adds unnecessary calls.
- Stateful Sessions: Storing session state on a specific server node breaks the stateless nature of microservices. If the user routes to a different node, the session is lost. Use external stores like Redis instead.
- Incorrect Error Codes: Returning specific error messages (e.g., “Invalid Password”) leaks information. Return generic errors like “Authentication Failed”.
- Ignoring Timeouts: If the Database is slow, the Authentication Service should not wait indefinitely. Implement a timeout threshold to fail fast.
- Hardcoded Endpoints: Services should not have hardcoded URLs for other services. Use service discovery mechanisms to find the correct instances dynamically.
🔄 Future-Proofing the Architecture
Standards and threats evolve. The login flow must be designed to accommodate changes without a complete rewrite.
- MFA Support: Design the sequence diagram to allow for a multi-factor authentication step. This means the Authentication Service can pause the flow and request a second code before issuing a token.
- OAuth Integration: If the system needs to support third-party logins (like SSO), the Gateway or Auth Service should act as an OAuth Client. The sequence diagram should show the redirect flow to the external provider.
- Decomposition: If the system grows, the Token Service might need to split into separate issuers for different client types (mobile vs. web). The diagram should be modular enough to accommodate this split.
🛠️ Maintenance and Evolution
Once the system is live, the sequence diagram is not static. It must be updated whenever the flow changes. This ensures that the documentation remains a source of truth.
- Version Control: Store the diagrams in the same repository as the code. This links design decisions to implementation.
- Change Logs: Document every modification to the login flow. If a new service is added, note why it was necessary.
- Testing: Use the diagram to create integration tests. Verify that the actual system matches the modeled flow.
- Audit Trails: Ensure the Authentication Service logs all login attempts. The logs should correlate with the sequence steps for debugging.
By treating the sequence diagram as a living document, teams can maintain high confidence in the system’s behavior over time. Regular reviews of the diagram against production metrics help identify bottlenecks or security drifts early.
📈 Monitoring the Flow
Visualizing the flow is only half the battle. You must also monitor it in production. Distributed tracing tools allow you to see the actual sequence of calls as they happen in real-time.
- Trace IDs: Assign a unique trace ID to every login request. This ID travels with the request through the Gateway, Auth Service, and Token Service.
- Metrics: Track the duration of each step. If the Token Service takes longer than expected, it might indicate a key generation bottleneck.
- Error Rates: Monitor the percentage of failed login attempts. A sudden spike might indicate a security attack or a configuration issue.
When the trace data deviates from the modeled sequence diagram, it warrants investigation. The diagram represents the intended path; the traces represent the reality. Aligning the two is key to system stability.
🎯 Summary of Best Practices
Building a secure and efficient login flow in a microservices environment requires careful planning and continuous attention. The following points summarize the core principles derived from this case study.
- Always use sequence diagrams to map out interactions before coding begins.
- Keep services stateless to ensure scalability and reliability.
- Separate credential verification from token generation for better security isolation.
- Implement strict rate limiting at the gateway level.
- Use short-lived access tokens and rotate refresh tokens.
- Monitor the actual flow against the designed model using distributed tracing.
- Update documentation whenever the architecture changes.
Following these guidelines ensures that the authentication system remains robust, secure, and maintainable as the platform grows. The complexity of microservices is manageable when the interactions are clearly defined and visualized.